The Benefits of Federated Id
The credentialing process — step by step review of what has been, what’s to come It may be reasonable to challenge assumptions and establish improvements in security, reduce risks, and gain efficiencies in operations around access control solutions and ID credentials. This article seeks to ask questions of the existing processes around identity, credentialing, and access control, enabling the airport security operations to consider new and emerging credential models. It is also an attempt to look into the future and see what changes may be coming that affect credentials used in an airport access control environment.
Identity proofing and badging is an expensive process. How can airport owner/operators improve this and reduce the risks of “unbadged individuals” in their facilities? A recent “Inside Airport Security” article (www.airportbusiness.com) by Art Kosatka, CEO of TranSecure, points out the real-world operational impacts of unbadged individuals who now must be escorted.
Escort is a huge issue — involving ID proofing, sponsorship, and training. But part of it is ID proofing and credentialing, and there are things that can be done to improve the decision time and service costs to establish identity. Whatever we do, if we can reduce the number of “unbadged individuals” by improving the process around badging and access decisions, we will have improved the operational efficiency and security of our facilities.
‘An Isolated Island’
The traditional view of credentialing and access control is an isolated island serving the airport owner/operator. It serves their local posture, and is in accord with their approved facility security plan. It is a narrow-world view.
Airport officials perceive that they must issue their own badge and manage its entire lifecycle. Across facilities, there is a fairly consistent process involved where access control begins with an application, identity proofing, and screening for every individual. Once approved, an applicant receives a badge that is printed with locally controlled security features and access designations as appropriate to management approved access privileges and roles.
This credential is then registered to the facility’s physical access control systems (PACS), enabling controlled automated access. This island-based process is effective, but it doesn’t account for anyone else working towards the same goal — a strong ID to enable access.
Federal initiatives in identity and credentialing may benefit airport operators in both cost of operations and the security of their facilities. There are many different communities of interest served by ID credentials that may impact access control operations. Intermodal operators, local police, fire and rescue partner programs, air crews, federal officials, concession services, all have ID credentials and seek access to local facilities.
The “ultimate objectives” of airport credentialing, whose objective is to provide secure and reliable access control, may be best achieved by looking at Federated ID and its opportunity to improve business operations.
The Basics: what we all do with credentials
All access control solutions operate in very similar manners at a process level. First, we establish some identity proofing of the individual and subsequently issue an appropriate token (badge) that is then registered to the access control system. Then the individual uses the token for access in daily operations. Finally, we consider “end of life” issues and failure modes that revoke access.
Registration for access starts it all, and typically involves the following core responsibilities:
- Present an application;
- Confirm identity of bearer;
- Confirm valid credential;
- Confirm management grant of access to requested system; and
- Bind credential to user in system, and grant role-based access.
The application for access starts the process. It typically identifies sponsorship and reasons for access to areas of the facility. The application is for an individual, and we need to confirm that the individual applying is the person described in the application. This typically follows the I-9 process for selecting identity credentials to confirm that the bearer matches the photo found on federal or state issued photo IDs.
Confirmation that the presented credentials are still valid and truly represent the bearer is difficult and may or may not be done beyond looking at the document to see if it is expired as printed on the ID. Once the application is reviewed and the bearer’s identity is confirmed through valid credentials, a management review begins. This includes a risk assessment (through the Transportation Security Clearinghouse process) and local authorization procedures (category of work role, areas appropriate to that role). Once all reviews are cleared, authorization is granted to issue a credential to the individual and grant access in the PACS.
In daily use by the individual, the credential is presented to the PACS, which does the following:
- Confirms credential is still valid;
- Confirms credential is unaltered/not forged/not copied;
- Confirms PIN and/or biometric, according to security policy; and
- Grant/deny, based on role (open door, login to system, etc.).
Confirmation that the credential is valid is typically done by two processes: visual inspection (photo matches bearer, expiration date) and electronic verification within the PACS. A more difficult process is confirmation that the credential is unaltered, forged, or copied. (Are any of us forensic document experts?)
Local policy then determines if bearer confirmation is required. This can be achieved using PIN codes or biometrics, as appropriate. If the credential is still valid and not altered, the bearer is matched according to policy, then access is granted according to role (open the door, drop the ramp gate, etc.).
The final consideration in operations is ‘end of life’ for the credential, for individuals whose credentials have been revoked:
- Revoke based on management directive;
- Revoke based on lost/stolen/damaged;
- Revoke based on expiration of privileges;
- Revoke on severance; or
- Revoke access if issuer revokes credential.
Local policies drive revocation management. Keeping clean records in an access control system for individuals is critical. Federal regulations, such as the five percent rule for credentials not accounted for, are driven by the need to ensure a secure and controlled access environment.
Federal ID Credentials
The President signed Homeland Security Presidential Directive #12 (HSPD-12) in August, 2004 to establish the need for secure identification credentials for all federal employees and contractors. The directive requires:
- ID issued based on sound criteria for verifying an individual employee’s identity;
- Strongly resistant to identity fraud, tampering, counterfeiting, and terrorist exploitation;
- Rapidly authenticated electronically;
- Issued only by providers whose reliability has been established by an official accreditation process.
Italics have been added to highlight critical issues in these directives consistent with the needs of aviation credentials. The core issues driving this directive include the ability to confirm who you are so a determination of access or information sharing can be made effectively.
Consider the front line individuals who locked down their buildings in New York City after the World Trade Center fell. If you did not have a locally issued ID badge to get into their building, you were locked out. In the heat of the moment, the idea that the local authority can evaluate that you truly are an FBI agent coming in from Washington, D.C. and that you should be granted access to the FBI offices in New York City is a difficult problem to solve.
HSPD-12 is intended to address this issue specifically. There is now a clear need for a reliable identity credential that can be operationally used locally as appropriate.
Given one of these credentials, it’s substantially easier to verify exactly who is standing in front of you and to which organization they belong. A local authority now has substantially better information on which to make a decision — that is, let the individual in or not.
From this directive, the National Institute of Standards and Technology (NIST) defined the Federal Infor-mation Processing Standard 201 “Personal Identity Verification (PIV) for Federal Employees and Contractors” (FIPS 201). This standard provides two core parts:
- Part I provides for identity proofing and issuance of PIV credentials;
- Part II provides requirements for the PIV credentials to enable interoperability between agencies
Part I provides the ability for anyone to establish an accreditable process for ID proofing and credential issuance. This is a big leap forward. FIPS 201 is recognized globally as the first standard that truly addresses the total issue around ID credentials. It provides a secure chain of trust between the identity proofing and issuance to a strong ID credential that is secure, interoperable, and operationally useful.
Step-by-Step Analysis
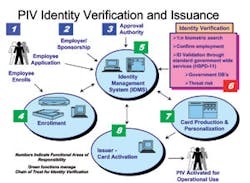
One of the approved processes in FIPS 201 is shown in Figure 1 - ID Verification and Issuance. This process shows the basic steps that are already done in aviation credentialing, but it shows it now as a cohesive process that anyone can use as appropriate to their local needs. It details the four critical areas for chain of trust management and issuance (steps 4, 5, 7, and 8). The core elements are:
- Enrollment — the individual submits an application, provides photo and biometrics, and presents documents supporting claim of identity. These are securely bound together for adjudication by the IDMS.
- The IDMS manages the ID proofing process and provides workflow, threat risk evaluation and credential management services.
- Upon approval, a card is produced for the individual.
- The card is then issued to the person for operational use.
There are many ways to design the topology of a compliant credential, but it may look like the one shown in Figure 2 - A sample PIV Card (there are many layout decisions one could make). Figure 3 shows two alternatives for consideration that come directly from the FIPS 201.
It’s critical to note that FIPS 201 describes how to get a credential and what it does, but it does not dictate operational use models. This is a local decision; there is no intention to interfere in local security designs that address local threats and risks.
As the government progresses along with this standard, its many successes impact additional programs that are of specific benefit to and/or impact to airport access control and operations.
The Transportation Worker Identification Credential (TWIC) and the First Responder Access Credential (FRAC) are both FIPS 201-compliant credentials. TWIC is initially being deployed to serve the maritime worker community. FRAC is currently being led and evaluated out of the National Capital Region and involves the Metropolitan Washington Airports Authority, state and local fire, law enforcement, and homeland security officials in a cooperative program with DHS.
If and when a TWIC may be required of airport workers, and if and when fire/rescue and police partners start participating with FRAC, makes for interesting discussion. But the benefits of looking at what they do and how it can improve airport access control and security must be considered.
A Cooperative Future
Consider Mr. Kosatka’s initial issue: new requirements for escorted access for unbadged personnel. Consider the President’s initiative to establish an interoperable ID credential that is secure, reliable, and resistant to tampering and alteration. Consider an airport’s normal operating procedures for access control, including initial identification of the individual, the grant of access, and subsequent end-of-life issues. What would happen if there was an interoperable credential that enabled local access decisions quickly and easily?
Federated ID is an opportunity to significantly reduce risks and improve security through consistent identity proofing and credentialing. A Federated ID response would lead to:
- I can prove who you are easily because you are using a FIPS 201-compliant ID credential
- I can determine that the credential is unaltered and is not expired or revoked by its issuer
Now I have essentially completed identity proofing and can determine if you should have access to a local facility. I may choose to issue you a local access badge, or if my PACS systems are enabled, I can register the credential you brought with you for access control.
At a minimum, federated ID allows an airport owner/operator to consider the following options:
- Shift the liability for identity proofing and credentialing to partners using an accredited process as guided by FIPS 201.
- Eliminate the need to run the full identity proofing process (time, labor, and cost intensive), as the partners have already done it. This transitions from hours/days/weeks into minutes, based on Federated ID using interoperable credentials.
- An airport may still have to augment the threat risk evaluation, as the requesting individual may or may not have appropriate training, skills, and need to access an area of the airport. This is specific to the role requested and situational need.
- Perhaps not have to issue a local badge, depending on access control policies. This may allow use of the credential the individual brings. (This is analogous to airline employee badges accepted for use within a tenant area operated by that airline.)
- Locally revoke access in a timely manner, as is normal within local facility procedures
Federated ID is a tool that enables smarter and safer access decisions based on secure ID policies and interoperability of the credential. Considering the impact of the security directives around unbadged individuals, it may be reasonable to consider Federated ID as an alternative approach. Federated ID enables us to reduce the number of unbadged individuals by honoring what they bring with them. Yes, they are badged. Yes, they have an assured identity. And finally, the access decision that enabled them to enter the area was a local decision.
Start looking into Federated ID. Plan for it. Pave the way. It may come sooner than expected.