Getting Identity Assurance Right
In my prior three articles for Airport Business, we focused on identity, credentialing, and supporting technologies and processes, with a focus on how these issues impact airport owner/operators, their operations, and their security posture. Given all this information, what is the state of the industry for Identity Assurance in airports? That is subject to be addressed here.
While attending the 2008 RSA Conference in San Francisco, the nation’s largest conference on information security that has grown (from the dot-bust era) into a behemoth again, I was struck by an emerging, common theme at this conference: Identity Assurance. Keynote addresses by EMC’s RSA Security Division, Microsoft, Symantec, and others all mention this as the underpinning of success. Identity Assurance was highlighted for access control, for e-Commerce, for employment, and everything in between. As I walked the show floor, vendors had Identity Assurance as one of the key features of their booth graphics, as well as how their products and services help you get it right.
Here are some questions I get asked often by airport security folks: “I already do identity and credentialing with my access control systems — can’t I just add biometrics for access control? Why isn’t this enough?”
Further, how will TSA, FAA, standards (such as RTCA DO-230B and FIPS 201), ACIS, and the emerging pilot programs by AAAE called BASIC all play out to improve our security posture? Is all this stuff necessary? What about those sunk costs in deployed investments for access control?
Again, why can’t I just add biometrics?
Many Parallel Events
There are currently several critical events happening in parallel from a standards and program point of view:
- 14.March.2008 — Federal Identity and Credentialing Committee’s architecture working group publishes the draft Back-End Attribute Exchange Architecture and Technical Specification (BAE Spec). (This will soon be made public at www.smart.gov/awg.)
- April.2008 — National Institute for Standards and Technology publishes Special Publication 800-116 (SP800-116) in draft form (available at www.csrc.nist.gov/groups/SNS/piv/standards.html).
- April.2008 — AAAE forms the Biometric Airport Security Identification Consortium (BASIC)
- 29.April.2008 — RTCA Special Committee 207 votes approval and completion of its work on the revisions to the DO-230A. This work is anticipated to publish as the DO-230B in June.2008. (Upon approval, it will be available at www.rtca.org.)
- 29.April.2008 - TSA publishes for airports its draft Aviation Credential Interoperability Solution (ACIS) Technical Specification to the aviation community. (Authorized users may visit http://webboards.tsa.dhs.gov for access.)
This is a tremendous amount of information all coming out roughly at the same time. If you are thinking information overload, you would be a member of a large club. Those of us in the Identity Management and Credential Issuance System (IdM-CIS) business see this as business as usual. This information gap must be resolved. So here are some thoughts on how to look at these documents.
The foundation of all of these documents and programs is Identity Assurance and the proper use of identity and credentials to establish a privilege (the right to access a facility or network). As seen in the commercial security vendor world at the RSA Conference, this is a top-of-mind issue. It is not a situation where a TSA regulation should drive us.
Intellectual property rights, critical business applications, and critical infrastructure protection all need robust identity assurance processes to mitigate security risks. As seen in the standards world for government employees and contractors, and for aviation, we see significant progress on using Identity Assurance as a critical component to protecting our facilities and personnel.
The RTCA DO-230B is thorough guidance on Integrated Security Systems for Airports in an access control environment (discussed in previous articles). It lays the foundation for positive access control solutions, starting with Identity Assurance and the IdM-CIS processes and Physical Access Control Systems (PACS). It also lays the foundation for defensive activities of video monitoring, intrusion detection.
And it completes the view with Security Operations for alerts and response management solutions.
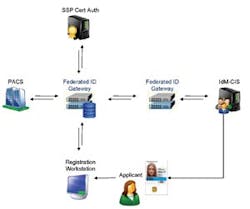
Figure 1 is extracted from Section 3 of the DO-230B discussing migration management. It shows the need for a Federated ID Gateway between a PACS and the IdM-CIS. So what is this gateway and what exactly does it do? We find the answers in the GSA’s BAE Specification. This specification provides standards based messaging (using SAML and SPML) to provide information needed to support the provisioning and de-provisioning processes.
NIST SP800-116 is an excellent work. As with all drafts, they are subject to change. Yet this document is quite well thought out. It fully describes the vision and technical means on how to use a FIPS 201 compliant PIV credential for physical access. This draft is open for public comment and it is an excellent read. Please do provide comments from the aviation perspective. It can only enhance the document.
SP800-116 provides insight into the risks of deployed access control badge media and systems and how interoperable PIV compliant solutions address these issues. It is an honest assessment of risks in today’s access control environment. As I read this document, I could not help but feel that we all, in our professional security lives, eventually make assumptions about risks and how acceptable they are to our business.
This publication certainly challenges complacency around our use of credentials and presents us with rational responses to security risks and issues they identify.
(For a really deep dive on attacks that make the risks identified in SP800-116 very realistic, look at the paper titled “Designing and implementing malicious hardware” by Samuel King, et.al., published at the Usenix conference in 2008, available at http://www.usenix.org/event/leet08/tech/full_papers/king/king.pdf.)
As good as the PIV credentials and the processes embodied by FIPS 201 and RTCA DO-230B are, we are not done yet. To emphasize how important interoperability is and how important trust in credentials is becoming, SP800-116 offers the following thoughts:
Interoperability of PIV Cards and FIPS 201 authentication mechanisms is not a guaranteed consequence of the technical standard. Government-wide interoperability also requires Federal agencies to exhibit reciprocal trust in the processes of PIV issuers and the service quality of the PIV Card validation and revocation infrastructure. Reciprocal trust is enabled by the requirements for the PIV issuance process stated in FIPS 201, and supported by the Certification and Accreditation (C&A) process methodology described in NIST SP 800-79. Trust is built when the technical standard is thorough, unambiguous, and grounded in practical requirements; when the conformance and audit processes are documented, trained, and uniformly practiced; and when positive PIV System audit results are available to the community of relying parties.
Identity Assurance is the foundation. Challenging our assumptions that we already “do it right” with credentialing in our PACS systems is now appropriate. There are formal processes to validate your assumptions. Using formal certification and accreditation of systems is proof positive that your assumptions are valid and your systems reflect your security needs.
SP800-116 also takes migration management seriously. It introduces the PIV Implementation Maturity Model (PIMM). There are always assets that deserve greater protection than others. The PIMM provides us with a model of migration from initial use of a PIV credential, all the way forward to a view where every access decision made is based on a PIV credential. No airport owner/operator, federal agency, or commercial entity can take on the full update of a new IdM-CIS and PACS model based on PIV without migration. The PIMM is one of the best models I’ve seen yet to guide security professionals forward to successful implementations.
State of various Programs
There are now two core activities, showing the urgency on this issue, around biometrics and access control in aviation:
- TSA’s Aviation Credential Interoperability Solution Program (ACIS); and
- AAAE’s Biometric Airport Security Identification Consortium (BASIC).
Both of these programs and their approaches leverage the successes learned from the Registered Traveler program, yet they take different approaches.
BASIC is a concept of voluntary participation for biometric access control leveraging the existing processes and infrastructure coming from airport systems in place already. It seeks minimal disruption, maximum return. Excellent primary goals.
ACIS took the technology of Registered Traveler and applied it in an open specification that enables Identity Assurance through an interoperable ID now. It is not a consortium, but a published specification that supports a consortium approach. It still needs industry input, but it is a good start.
ACIS should be music to the BASIC consortium’s ears, yet coming from TSA, it may not gain a warm reception. As with all drafts, this is subject to change, yet it provides a view of Identity Assurance and the IdM-CIS process that is substantially in harmony with the RTCA DO-230B. Given that the Registered Traveler model influenced all three activities (BASIC, ACIS, and DO-230B), it is not hard to see how this confluence occurred.
Per the specification published for ACIS, it presents a three-step model:
- Identity Assurance and Identity Credential Issuance;
- Identity Assurance and Identity Credential Issuance with Electronic Identity Verification; and
- Identity Assurance and Identity Credential Issuance with Electronic Identity Verification and a Privilege Application for access control.
This three step model provides for the transition, as described in the RTCA DO-230B, in a controlled and consistent manner. It is substantially in harmony with NIST SP800-116’s concept of PIV Implementation Maturity Model. It shows a gradual adoption of using an identity credential and growth into physical access solutions.
Figure 2 is also extracted from the RTCA DO-230B’s section 3 on migration for IdM-CIS. Putting this all together may not be as hard as we thought. This figure is not quite perfect, but it is very close. If we assume the IdM-CIS shown in the figure issues an ACIS compliant Identity Credential (in accord with ACIS Phase I), then an applicant using that credential in the Registration Workstation will be providing high assurance identity information to the PACS. Identity information from that ACIS credential is parsed and used to provide for the initial record in the PACS. This substantially improves identity assurance for that applicant within our PACS. From there, you complete the enrollment process according to local policy, issuing an airport specific local identity card or access credential. Therefore the bearer has an ACIS ID card and an access media issued by the airport operator, and possibly a third item — an identity card issued by the airport operator.
The ACIS specification does a couple of interesting things. For an ACIS-compliant credential issued by the local airport, the airport has full authority to define the topology of the credential. The credential topology defined in Appendix D of ACIS is only for aircraft operators (in particular, airlines) that issue their own ID credentials. This is a critical distinction.
Another very interesting opportunity presented by early phases of ACIS are specifications for contact chip operations only. It does NOT specify contactless operations until Phase III. A business case could be made that adding a standard contactless inlay (e.g., HID Prox, iClass or solutions using a DESfire chip) to an ACIS credential would enable local airport owner/operator controlled contactless access control operations. (This may be the model to avoid having two badges at an airport: one for identity according to ACIS and one for access per the local access system’s requirements.)
As the BASIC consortium has not published its specifications and intentions, it’s not quite as easy to see how this will work. Yet the tenets found in the Registered Traveler Interoperability Consortium are good guides: an open process, with open specifications, enabling vendor and service provider competition to meet the needs of airport owner/operators.This process yielded a working result that is operating successfully at airports today. AAAE’s RTIC clearly demonstrated the ability of a consortium to deliver a working technical model that is secure and interoperable. Open specifications, as done by RTIC for Registered Traveler, will be critical to the success of BASIC. If they successfully leverage the standards and create a focused, interoperable solution for Identity Assurance and access control, all parties will benefit.
Time to step up
We have seen a real transition in government standards and commercial enterprise behaviors. Identity Assurance is front and center. Who we grant access to our facilities is critical to the security and integrity of our facilities and networks. Lessons learned on the Internet around identity theft have clarified in everyone’s mind that identity is very different than access, yet identity and the now dominant issues around Identity Assurance drive everything we do in access control.
The ACIS specification published by TSA may not be perfect, but it is an excellent starting point. Another way to summarize it is to say that it enables:
- Identity Assurance, through a standardized ACIS credential and trust model, supporting local decisions for access control;
- Field challenge programs for identity within an airport; and
- Over time, the opportunity for an interoperable access tool.
Identity Assurance tools and technology are available. The risks are real. Leverage investment and focus on a migration management plan to update according to risk and need.